Openssl Generate Key And Self Signed Certificate
- Openssl Generate Key And Self Signed Certificate Template
- Openssl Create Self Signed Certificate And Private Key
You can use the OpenSSL toolkit to generate a key file and Certificate Signing Request (CSR) which can then be used to obtain a signed SSL certificate. Steps to generate a key and CSR. To configure Tableau Server to use SSL, you must have an SSL certificate. To obtain the SSL certificate, complete the steps: Set the OpenSSL configuration environment variable (optional). Generate a key file. Sep 11, 2018 Option 5: Generate a Self-Signed Certificate from an Existing Private Key and CSR If you already have a CSR and private and need to generate a self-signed certificate, use the following command: openssl x509 -signkey domain.key -in domain.csr -req -days 365 -out domain.crt.
| # Define where to store the generated certs and metadata. |
| DIR='$(pwd)/tls' |
| # Optional: Ensure the target directory exists and is empty. |
| rm -rf '${DIR}' |
| mkdir -p '${DIR}' |
| # Create the openssl configuration file. This is used for both generating |
| # the certificate as well as for specifying the extensions. It aims in favor |
| # of automation, so the DN is encoding and not prompted. |
| cat >'${DIR}/openssl.cnf'<<EOF |
| [req] |
| default_bits = 2048 |
| encrypt_key = no # Change to encrypt the private key using des3 or similar |
| default_md = sha256 |
| prompt = no |
| utf8 = yes |
| # Speify the DN here so we aren't prompted (along with prompt = no above). |
| distinguished_name = req_distinguished_name |
| # Extensions for SAN IP and SAN DNS |
| req_extensions = v3_req |
| # Be sure to update the subject to match your organization. |
| [req_distinguished_name] |
| C = US |
| ST = California |
| L = The Cloud |
| O = Demo |
| CN = My Certificate |
| # Allow client and server auth. You may want to only allow server auth. |
| # Link to SAN names. |
| [v3_req] |
| basicConstraints = CA:FALSE |
| subjectKeyIdentifier = hash |
| keyUsage = digitalSignature, keyEncipherment |
| extendedKeyUsage = clientAuth, serverAuth |
| subjectAltName = @alt_names |
| # Alternative names are specified as IP.# and DNS.# for IP addresses and |
| # DNS accordingly. |
| [alt_names] |
| IP.1 = 1.2.3.4 |
| DNS.1 = my.dns.name |
| EOF |
| # Create the certificate authority (CA). This will be a self-signed CA, and this |
| # command generates both the private key and the certificate. You may want to |
| # adjust the number of bits (4096 is a bit more secure, but not supported in all |
| # places at the time of this publication). |
| # |
| # To put a password on the key, remove the -nodes option. |
| # |
| # Be sure to update the subject to match your organization. |
| openssl req |
| -new |
| -newkey rsa:2048 |
| -days 120 |
| -nodes |
| -x509 |
| -subj '/C=US/ST=California/L=The Cloud/O=My Company CA' |
| -keyout '${DIR}/ca.key' |
| -out '${DIR}/ca.crt' |
| # |
| # For each server/service you want to secure with your CA, repeat the |
| # following steps: |
| # |
| # Generate the private key for the service. Again, you may want to increase |
| # the bits to 4096. |
| openssl genrsa -out '${DIR}/my-service.key' 2048 |
| # Generate a CSR using the configuration and the key just generated. We will |
| # give this CSR to our CA to sign. |
| openssl req |
| -new -key '${DIR}/my-service.key' |
| -out '${DIR}/my-service.csr' |
| -config '${DIR}/openssl.cnf' |
| # Sign the CSR with our CA. This will generate a new certificate that is signed |
| # by our CA. |
| openssl x509 |
| -req |
| -days 120 |
| -in '${DIR}/my-service.csr' |
| -CA '${DIR}/ca.crt' |
| -CAkey '${DIR}/ca.key' |
| -CAcreateserial |
| -extensions v3_req |
| -extfile '${DIR}/openssl.cnf' |
| -out '${DIR}/my-service.crt' |
| # (Optional) Verify the certificate. |
| openssl x509 -in '${DIR}/my-service.crt' -noout -text |
| # Here is a sample response (truncate): |
| # |
| # Certificate: |
| # Signature Algorithm: sha256WithRSAEncryption |
| # Issuer: C = US, ST = California, L = The Cloud, O = My Organization CA |
| # Subject: C = US, ST = California, L = The Cloud, O = Demo, CN = My Certificate |
| # # .. |
| # X509v3 extensions: |
| # X509v3 Basic Constraints: |
| # CA:FALSE |
| # X509v3 Subject Key Identifier: |
| # 36:7E:F0:3D:93:C6:ED:02:22:A9:3D:FF:18:B6:63:5F:20:52:6E:2E |
| # X509v3 Key Usage: |
| # Digital Signature, Key Encipherment |
| # X509v3 Extended Key Usage: |
| # TLS Web Client Authentication, TLS Web Server Authentication |
| # X509v3 Subject Alternative Name: |
| # IP Address:1.2.3.4, DNS:my.dns.name |
| # |
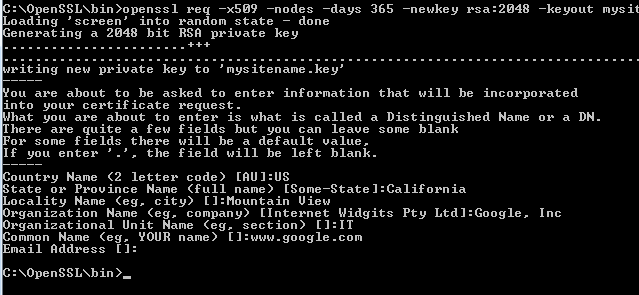
Generating a self-signed certificate with OpenSSL: Win32 OpenSSL v1.1.0+ for Windows can be found here. Open Windows File Explorer. Navigate to the OpenSSL bin directory. C:OpenSSLbin in our example. Right-click the openssl.exe file and select Run as administrator. You must update OpenSSL to generate a widely-compatible certificate' The first OpenSSL command generates a 2048-bit (recommended) RSA private key. The second command generates a Certificate Signing Request, which you could instead use to generate a CA-signed certificate. This step will ask you questions; be as accurate as you like since you probably aren’t getting this signed by a CA. Create a root CA certificate. Create your root CA certificate using OpenSSL. Create the root key. Sign in to your computer where OpenSSL is installed and run the following command. This creates a password protected key. Openssl ecparam -out contoso.key -name prime256v1 -genkey At the prompt, type a strong password. All necessary steps are executed by a single OpenSSL invocation: from private key generation up to the self-signed certificate. Remark #1: Crypto parameters Since the certificate is self-signed and needs to be accepted by users manually, it doesn't make sense to use a short expiration or weak cryptography.
Updated by LinodeWritten by Linode
Report an Issue View File Edit File
Windows 10 pro product key generator online 2018. Dec 19, 2017 When you Upgrade to Windows 10 from Windows 7, even you can use Windows 10 Professional Product Key Generator. Best Top 10 Tech Websites 2018 Everyone Should Know Get Free Windows 10 Professional Product Key Generator. For example, you have Windows 7 product key; now you want to upgrade to Windows 10 for Windows 10 Professional Product Key.
What is a Self-Signed TLS Certificate?
Self-signed TLS certificates are suitable for personal use or for applications that are used internally within an organization. If you intend to use your SSL certificate on a website, see our guide on enabling TLS for NGINX once you’ve completed the process outlined in this guide.

Openssl Generate Key And Self Signed Certificate Template
Create the Certificate
Change to the
rootuser and change to the directory in which you want to create the certificate and key pair. That location will vary depending on your needs. Here we’ll use/root/certs:It is combined with security, manageability, the reliability of Windows 2000, user-friendly, plug and play, the graphical consumer interface of Windows XP. Moreover, it is also approved to be built at the Windows NT Kernel. Windows xp sp3 product key generator download for pc. Easy steps to find a version of Windows XP installed on your laptop:. Apart from the few professionals and cons, the Windows XP could be very easy to use.
Create the certificate:
You will be prompted to add identifying information about your website or organization to the certificate. Since a self-signed certificate won’t be used publicly, this information isn’t necessary. If this certificate will be passed on to a certificate authority for signing, the information needs to be as accurate as possible.
The following is a breakdown of the OpenSSL options used in this command. There are many other options available, but these will create a basic certificate which will be good for a year. For more information, see
man opensslin your terminal.-newkey rsa:4096: Create a 4096 bit RSA key for use with the certificate.RSA 2048is the default on more recent versions of OpenSSL but to be sure of the key size, you should specify it during creation.-x509: Create a self-signed certificate.-sha256: Generate the certificate request using 265-bit SHA (Secure Hash Algorithm).-days: Determines the length of time in days that the certificate is being issued for. For a self-signed certificate, this value can be increased as necessary.-nodes: Create a certificate that does not require a passphrase. If this option is excluded, you will be required to enter the passphrase in the console each time the application using it is restarted.
Here is an example of the output:
Restrict the key’s permissions so that only
rootcan access it:Back up your certificate and key to external storage. This is an important step. Do not skip it!
Join our Community
Openssl Create Self Signed Certificate And Private Key
This guide is published under a CC BY-ND 4.0 license.